Disclose and identify all Common Vulnerabilities and Exposures (CVE) within the affected endpoints to prioritize and manage patching procedures before malicious exploitation by threat actors.
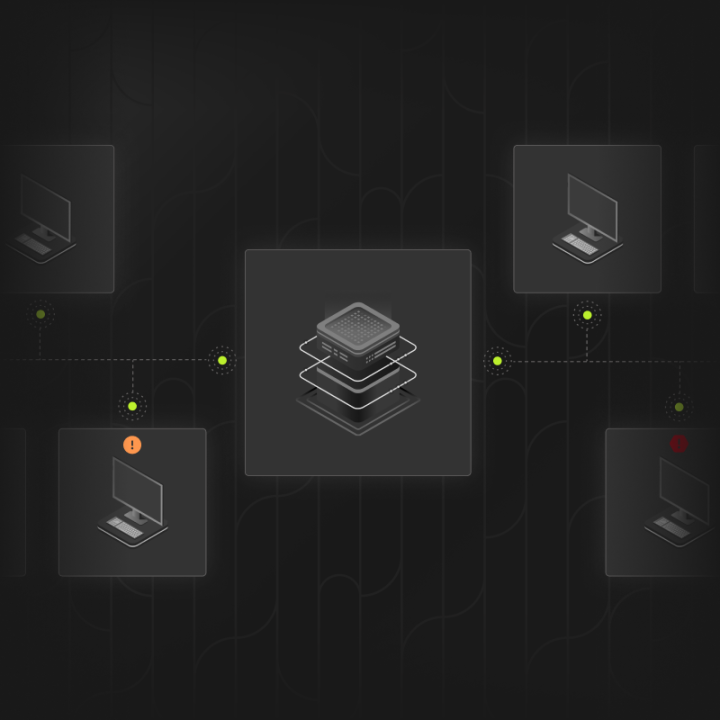
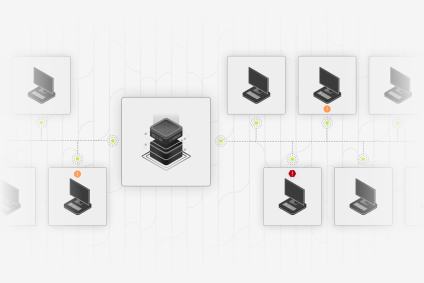
- Use a single endpoint agent for continuous and frictionless monitoring rather than launching heavy, manual scans
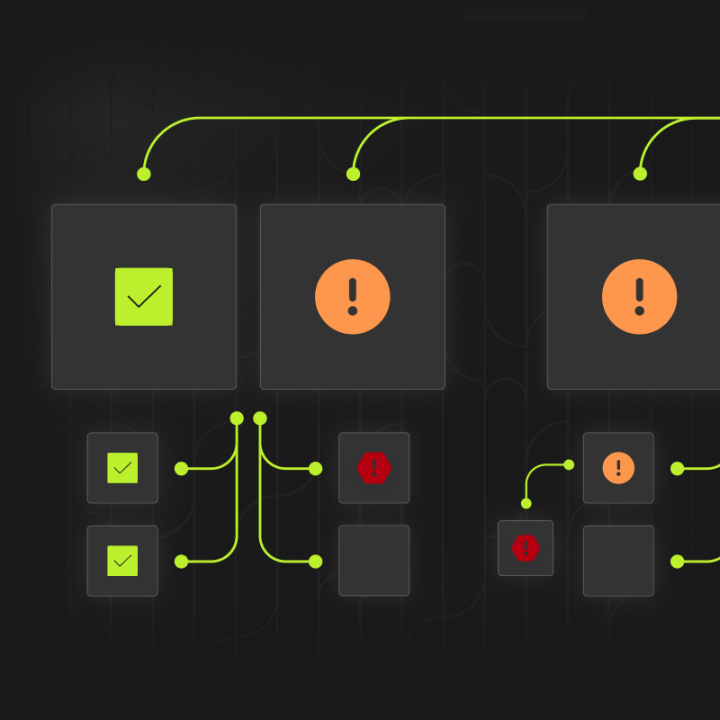
- Detect vulnerabilities in OSes and applications
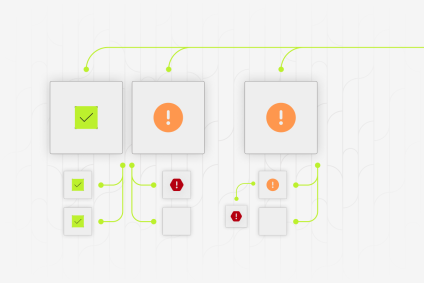
- List endpoints and applications that need patching and mitigation
- Correlate data from your security platform and tools to respond faster to threats